Search results for tag #cybersecurity
This dumb password rule is from URSSAF (French employers tax collection service).
When setting a new password:
Password must be exactly 8 characters, at least 1 letter, at least 1 number, but no special characters.
https://dumbpasswordrules.com/sites/urssaf-french-employers-tax-collection-service/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Ancestry.
Password:
- Must be at least 8 characters long
- Must contain at least 1 number
- Must contain at least 1 letter or special character
- Must not be a well known or common password
https://dumbpasswordrules.com/sites/ancestry/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
Insider trading isn't just a Wall Street problem anymore. A Google information security engineer allegedly used privileged access to internal data to place bets on Polymarket, netting around $1 million.
Read more: https://steelefortress.com/bhouop
CyberDefense #Cybersecurity #ThreatIntel #Encryption
This dumb password rule is from URSSAF (French employers tax collection service).
When setting a new password:
Password must be exactly 8 characters, at least 1 letter, at least 1 number, but no special characters.
https://dumbpasswordrules.com/sites/urssaf-french-employers-tax-collection-service/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Chegg.
Here are the (only fairly poor) rules for a new password. Enter 64 character password that matches all the rules (notice no rules on maximum length). That password you entered looks good! But we didn't change it. And your old password doesn't work. Or the new one. ¯\\\_(ツ)\_/¯
https://dumbpasswordrules.com/sites/chegg/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
Hey Fediverse, I’m looking for a new role, preferably remote.
I’m an IT/MSP/cybersecurity professional with leadership experience in managed services, security operations, Microsoft 365, Entra ID, endpoint security, RMM/EDR, documentation, automation, service delivery, and client-focused IT strategy.
I’m especially interested in roles such as IT Manager, Security Operations Manager, MSP Operations Manager, Service Delivery Manager, Technical Operations Manager, Cybersecurity Program Manager, or similar leadership-focused positions.
BSIT + Associate C|CISO.
CV: https://cv.kylereddoch.me/
Boosts appreciated.
#FediHire #FediHelp #GetFediHired #Cybersecurity #InfoSec #MSP #ITManagement #RemoteWork
This dumb password rule is from Wells Fargo Identity Theft Protection.
Your password on an Identity Theft Protection service is limited to
between 8 and 20 characters. Your username is allowed to be longer than
your password.
https://dumbpasswordrules.com/sites/wells-fargo-identity-theft-protection/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Crédit Mutuel de Bretagne.
Password must be 10-16 characters with at least one letter, one number and no special character.
https://dumbpasswordrules.com/sites/credit-mutuel-de-bretagne/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from PizzaHut.
Passwords must be greater than 6 characters, and have an arbitrary set of rules we don't tell you about until after you try to set your password.
https://dumbpasswordrules.com/sites/pizzahut/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Discovery Benefits.
Requires at least one symbol, but must be one of `! @ # $ % & * ?`, and also
has an unstated max length of 20 characters.
https://dumbpasswordrules.com/sites/discovery-benefits/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
The dutchies have a centralized identity that you are using to basically interact with everything government. That contains pensions and health related issues.
This is called DigID. It is run by a company called Solvinity an was was supposed to be taken over by a U.S. company called Kyndryl.
The dutch cabinet (= government) has now blocked this takeover.
I think the topic of souvernty is slowly landing in the right heads. I guess also ... thank you @bert_hubert and everyone else making noise there🙂
#infosec #cybersecurity #souveraeneInfrastruktur #sovereignty #digid
This dumb password rule is from NBank.
User ID *has to* contain special characters, password *may not* contain (basically) any special characters.
https://dumbpasswordrules.com/sites/nbank/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
@EUCommission PLEASE force companies to release flatpak packages alongside their windows and macos packages!
secureblue is the only OS on the desktop when my data really belongs to only me.
Please force them to support Linux via flatpak.
#Linux #EU #privacy #security #cybersecurity #flathub #flatpak #data #MyDataMyChoice #FuckTheGovernment #Anarchy #Anarchism
This dumb password rule is from Inria.
This is the account for those who work at [Inria](https://www.inria.fr/)
"the French national research institute for
the digital sciences".
You have to wonder what's wrong with these special characters but not
the other ones.
- Password expiration once a year
- Your password must contain at leas...
https://dumbpasswordrules.com/sites/inria/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
🕵🏻♂️ [InfoSec MASHUP] 21/2026 - The Supply Chain Didn't Break. It Was Walked.
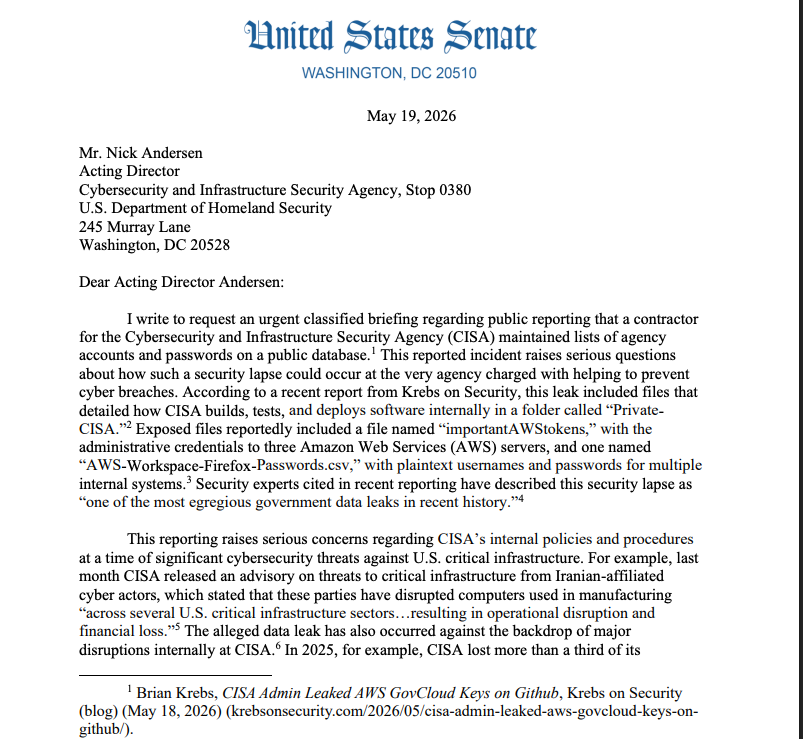
This week's issue reads like a case study in cascade failure. A malicious VS Code extension on one #GitHub employee's device leads to 3,800 internal repositories exfiltrated — by #TeamPCP, the same group that poisoned 170 npm and #PyPI packages last week. #Grafana gets breached via a token nobody rotated after the TanStack attack, itself a TeamPCP operation. A GitHub Action used by thousands of projects gets compromised and starts exfiltrating CI/CD credentials. And somewhere in a public GitHub spreadsheet, CISA contractor credentials — including #AWS GovCloud keys — sat waiting to be found.
These aren't four separate incidents. They're one incident with four manifestations. The supply chain isn't a vector anymore; it's the terrain. Developer tooling, CI/CD pipelines, third-party actions, tokens issued and forgotten — all of it is now actively mapped and exploited with a persistence that makes the traditional "patch and move on" response look quaint. The Verizon DBIR dropped this week noting that third-party compromise is surging. The week's news was already illustrating the point before the report landed.
→ Week #21/2026 also covers: fast16 predated #Stuxnet and corrupted nuclear simulations quietly, #Pwn2Own Berlin paid $1.3M for 47 bugs, and #Bluesky got hijacked for Russian propaganda.
Full issue 👉 https://infosec-mashup.santolaria.net/p/infosec-mashup-21-2026-the-supply-chain-didn-t-break-it-was-walked
If you find it useful, subscribe to get it in your inbox every weekend 📨 #infosecMASHUP #cybersecurity #infosec #threatintel #AI
This dumb password rule is from AirAsia.
- Between 8 and 16 characters
- Must contain a number, a lowercase letter, and an uppercase letter
- Special characters allowed, but not periods, commas, tildes, or angle brackets
https://dumbpasswordrules.com/sites/airasia/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from University of Western Australia (Pheme).
Passwords:
1. Must contain at least 8 characters;
2. Must contain at least 3 out of 4 types of characters
(uppercase letters, lowercase letters, digits, special characters);
and
3. Must not contain
"the user's account name or parts of the user's full name
that exceed two consecutive characters".
...
https://dumbpasswordrules.com/sites/university-of-western-australia-pheme/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Zurich.
Password must be EXACTLY 8 characters long.
Alpha numeric characters ONLY.
The first character must be alphabetic.
NO spaces.
The new Password cannot be the same as the last 32 passwords you have used. (they actually store your last 32 passwords)
https://dumbpasswordrules.com/sites/zurich/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Comcast.
Your password should be difficult to guess as long as it's not over 16
characters long.
https://dumbpasswordrules.com/sites/comcast/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
Ubiquiti Issues Emergency Patches for Five Critical UniFi OS Vulnerabilities, Three Rated Maximum CVSS 10.0
#CyberSecurity
https://securebulletin.com/ubiquiti-issues-emergency-patches-for-five-critical-unifi-os-vulnerabilities-three-rated-maximum-cvss-10-0/
This dumb password rule is from STOVE.
- 24 characters max
https://dumbpasswordrules.com/sites/stove/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
We’re proud to share that the FreeBSD Foundation has joined the Open Source Security Foundation (OpenSSF) as an Associate Member.
We look forward to collaborating with the OpenSSF community to strengthen the resilience and sustainability of open-source security worldwide.
Read the full announcement from the Linux Foundation:
https://www.linuxfoundation.org/press/openssf-notes-quarter-of-growth-with-new-members-added-ai-security-resources-and-growing-community
This dumb password rule is from CENLAR.
Your password can meet all the requirements in the list and still be invalid due to
an unspecified rule: any "special characters" that are not listed in the help text
are not allowed. Worse, it provides no useful feedback other than the "New Password"
field is red.
https://dumbpasswordrules.com/sites/cenlar/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
#Signalapp doesn't actually delete messages when they're deleted (either manually or by automation). The message deletion is written to Write-ahead Log, and the data is only truly deleted once Signal is restarted or threshold of 1000 pages is reached. For macOS Signal application, extra complication arises from the fact that the signal message database can be backed up before the database consolidation occurs. Large amount of the supposedly already deleted messages could be recovered from the device or backups.
This concerns use cases where deleting messages actually getting removed in timely manner is of high importance and recovery of the deleted messages could lead to grave consequences.
TL;DR: If you don't care about deleted messages being actually deleted you don't need to worry.
Full advisory at: https://sintonen.fi/advisories/signal-deleted-but-not-forgotten.txt
Oh.
Oh no.
but why?
How the *beep* has this ever worked?
Famous conversations in Information security.
This dumb password rule is from LCL.
You have to enter your 6-digit password using this Frenchy keypad.
https://dumbpasswordrules.com/sites/lcl/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Australia Immi Platform.
The Australian immigration platform requires at least 14 characters and at least one from three of the four groups: lowercase letters, uppercase letters, digits, and special characters.
The random generator in my password manager only needed one second attempt to avoid 'dangerous' special charact...
https://dumbpasswordrules.com/sites/australia-immi-platform/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Gigabyte RMA system.
Your password must contain:
Between 8-12 characters
An upper case letter (A, B, C, etc.)
a lower case letter (a, b, c, etc.)
A number (1, 2, 3, etc.)
A symbol (-, ~, !, #, $, %, &, (, ), +, =, .)
https://dumbpasswordrules.com/sites/gigabyte-rma-system/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
Check it: Sen. Maggie Hassan (D-NH) is demanding answers from CISA and DHS over my reporting this week that a CISA contractor had published on GitHub a number of CISA AWS GovCloud keys and a ton of plaintext passwords, SSH keys, etc. for internal CISA resources.
ICYMI:
https://krebsonsecurity.com/2026/05/cisa-admin-leaked-aws-govcloud-keys-on-github/
This dumb password rule is from Thames Water.
Can only use the "special" characters on that very limited list, excluding symbols so exotic as an underscore, even. This is despite their own strength checker saying the password is strong.
https://dumbpasswordrules.com/sites/thames-water/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
So question:
"how many authoritative name servers don't support encryption?"
The internet claims that this is >95%.
My personal feeling is that this is lower but this might be my bubble, that we're the 5%.
What's your feeling?
#infoSec #cybersecurity #DNS #encryption
Plz retoot for reach.
| It is our bubble. We're the 5%, noone else cares: | 10 |
| I think it is higher now - a bit, maybe 10% or so: | 5 |
| It is significantly higher - more 25%: | 0 |
| what the hell is DNS query encryption?: | 16 |
Closed
If you're using traffic lights at work to show the security status - this is your traffic lights to be used now.
This dumb password rule is from Battle.net.
8 to 16 characters, at least one number and one letter and last but not least NO special characters, and can't have a password that looks like your username too. Oh, and passwords are NOT case sensitive.
A real time travel adventure through the password rules of 2005!
https://dumbpasswordrules.com/sites/battle-net/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
Before you worry about #AI threats, fix your security fundamentals: Most cyber breaches aren’t driven by advanced AI - they’re caused by basic failures like exposed cloud storage and poor data governance. It’s time to refocus on #cybersecurity fundamentals.
https://katecarruthers.com/ai-threats-fix-your-security-fundamentals/
This dumb password rule is from INSS (Instituto Nacional do Seguro Social).
The National Social Security Institute (INSS) is an autarchy of the Government of Brazil linked to the Ministry of Economy that receives the contributions for the maintenance of the General Social Security System, responsible for the payment of pensions, maternity pay, death pay, sickness pay, ac...
https://dumbpasswordrules.com/sites/inss-instituto-nacional-do-seguro-social/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Aruba Cloud.
Must be different from the last 3 passwords used.
Your password must contain at least an uppercase and lowercase letter and number.
Must contain at least one special symbol.
https://dumbpasswordrules.com/sites/aruba-cloud/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
This dumb password rule is from Digital Credit Union (DCU).
Must be between 8 and 40 characters, uppercase and lowercase, one number, one special character... whatever. But special characters are limited to -#$%+?~*!. (and space). WHY?!
https://dumbpasswordrules.com/sites/digital-credit-union-dcu/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
Linux Torvalds says AI vuln research breaks the Linux security / development process.
#infosec #cybersecurity #linux #itstheendoftheworldandweknowit #andifeelfine
If you have not read the notes on security by microsoft from last tuesday you should.
https://www.microsoft.com/en-us/msrc/blog/2026/05/a-note-on-patch-tuesday
Update your shit. Windows, Linux .... keep all the systems up to date.
NIST has given up on CVE's. They can't deal with it anymore.
https://www.nist.gov/news-events/news/2026/04/nist-updates-nvd-operations-address-record-cve-growth
#NIST is from now on only reviewing "important" CVE's.
This means that only if it affects the (us) government or its really bad they will review CVE Submissions.
Around 90% of the submissions will not be reviewed anymore (for now)
This dumb password rule is from Alibaba.
- At least 2 uppercase letters
- Plus 2 lowercase letters
- Plus 2 numbers
- Plus 2 punctuation marks
Phew, too many rules, because why not, if [Ma thinks AI stands for Alibaba Intelligence](https://www.youtube.com/watch?v=f3lUEnMaiAU),
then password rules can be equally intelligent too.
Also, ...
https://dumbpasswordrules.com/sites/alibaba/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
How does Fedora process patches for security vulnerabilities? The short answer is that we work to stay on top of the news to implement patches, working in the community and with Red Hat for updates.
The long answer: https://fedoramagazine.org/how-fedora-is-responding-to-recent-kernel-vulnerabilities/
At the end of the day, the best thing you can do is keep your system updated. :)